Analytical Forensics
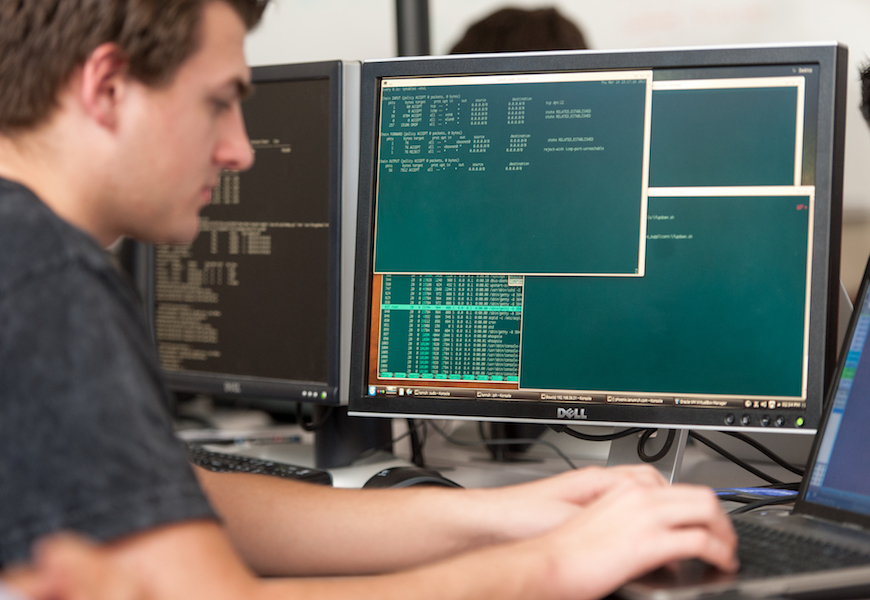
The problem of how to comb through large amounts of data produced from a computer network to identify with high-confidence breaches and misuses remains a hard problem in practice...
Start from REAL problems
Create solutions that LAST

















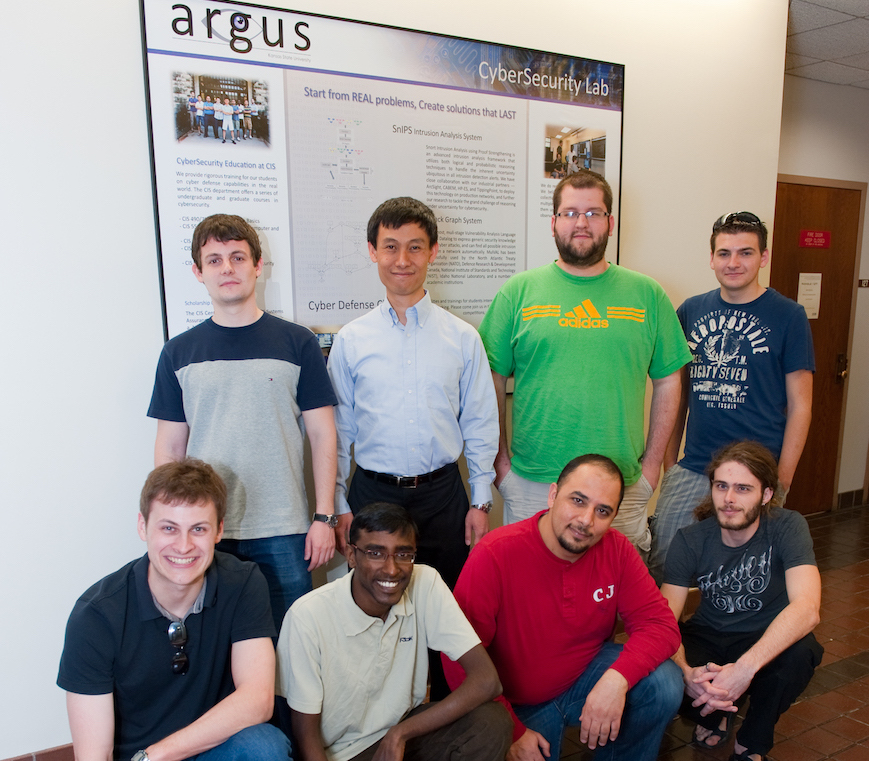
The Argus group was founded by Dr. Xinming (Simon) Ou in 2006 to carry out cyber security research. Our focus is on the defense aspect of the cyber space, and our philosophy is to start from real problems, and create solutions that last. Our research attempts to address the root causes of the various cybersecurity problems, and we work closely with industry to ensure our work both addresses the most pressing problems of the time, and provides the scientific basis for solutions that can stand the test of time.
We believe that successful cyber defense can only be achieved through automated coordination of various observation and action points in a network environment, and through fundamentally changing the way IT systems are created and managed to obviate the many security problems we face today. "Point solutions" like firewalls and traditional IDS systems are limited in effectiveness since they only look at one aspect of the system and lack the analytic capability of "connecting the dots" among various information sources. Moreover, they tend to focus more on dealing with the manifested problems rather than eradicating their root causes. Our research aims at providing the enabling technologies for automated security analytics, with solid theoretical foundation and empirical study. We also investigate ground-breaking new security technologies that could fundamentally change the game of cyber warfare to defender's advantage.
Argus research has been supported by the National Science Foundation, Department of Defense, Department of Homeland Security, Department of Energy, National Institute of Standards and Technology, and HP Labs. The group is named after the giant Argus in Greek mythology, who has a hundred eyes that constantly watch for enemies.
We start from REAL problems, and create solutions that LAST.
The problem of how to comb through large amounts of data produced from a computer network to identify with high-confidence breaches and misuses remains a hard problem in practice...
We conduct research to apply static analysis on Dalvik byte code of both Android applications and libraries, for the purpose of identifying potential malicious behaviors or program vulnerabilities.
This research applies anthropological methods to study cybersecurity analysts working in Security Operation Centers (SOC). These analysts process large amounts of data while handling cyber threats.
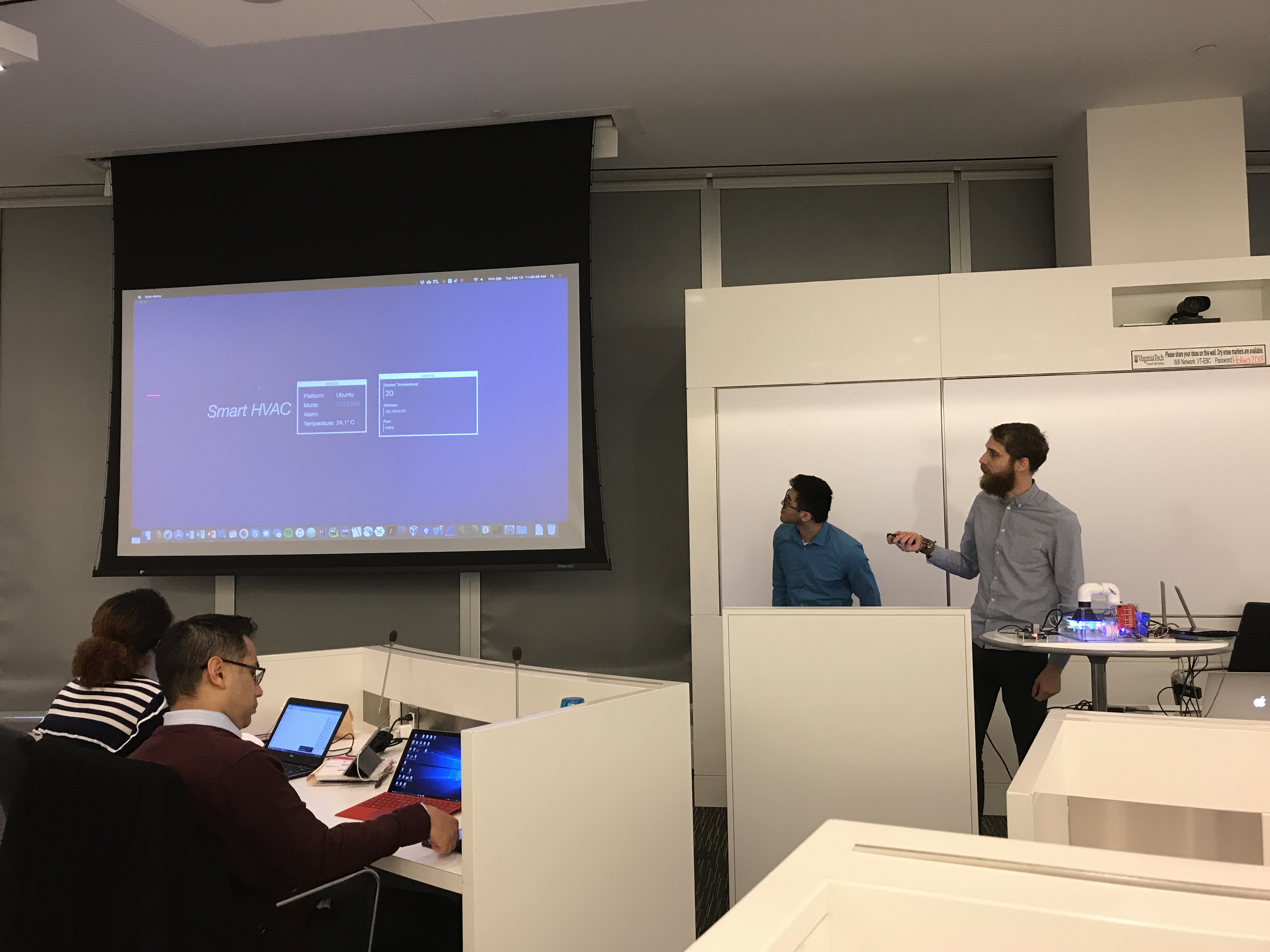
Next-generation embedded controllers for cyber-physical systems will be based on a "smart" platform. Some of the apps will bear responsibility to the safety of the physical systems being...
Cloud computing has the potential to revolutionize the way businesses run their IT infrastructure and achieve new efficiencies of scale. However, security and long-term trustworthiness...
The goal of this research is to understand and quantify the potential and limitations of moving-target defense (MTD) systems to protect computer networks. To achieve this goal, we are...
Argus-SAF is a Static Analysis Framework that we build in house to do security vetting for Android applications. It integrated two of our previously developed products Argus-Jawa and Argus-Amandroid, and have the capability to perform comprehensive, efficient and highly precise Inter-component Data Flow Analysis.
Moving Target Defense for Cloud-Based IT Systems (MTD CBITS) is a platform that automatically adapts multiple aspects of the network’s logical and physical configuration. The platform is targeting a cloud infrastructure and is built on top of ANCOR. ANCOR is a framework for creating and managing cloud-based IT systems using a high-level abstraction (an up-to-date IT system inventory).
SnIPS (Snort Intrusion Analysis using Proof Strengthening) works by mapping a Snort alert into a logic predicate describing the condition a user really cares about (e.g. machine compromised), along with a tag indicating the strength of the belief. The tagged conditions are reasoned about together and beliefs with strong corroborative evidential support are distinguished from those with only mediocre evidence, yielding high-confidence correlation graphs.
MulVAL stands for "Multi-host, multi-stage Vulnerability Analysis Language". It is a research tool for security practitioners and system administrators to better manage the configuration of an enterprise network such that the security risks are appropriately controlled.
Android Malware Dataset is a carefully-labeled and well-studied dataset that includes comprehensive profile information of malware. The dataset provides an up-to-date picture of the current landscape of Android malware, and is publicly shared with the community.
Professor
xou at usf dot edu
PhD Candidate
guojunl at mail dot usf dot edu
PhD Student
kshashwat at usf dot edu